Categories
Problems that solves
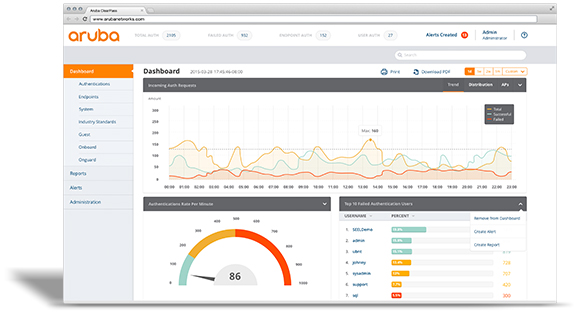
Unauthorized access to corporate IT systems and data
Malware infection via Internet, email, storage devices
Values
Ensure Security and Business Continuity
Description
CounterACT agentless technology discovers, classifies and assesses devices. CounterACT interrogates the network infrastructure to discover devices as they connect to the network. Our customers have reported seeing up to 60% more devices on their network than previously known. After discovering a device, CounterACT uses a combination of passive and active methods to classify the device according to its type and ownership. Based on its classification, CounterACT then assesses the device security posture and allows organizations to set policies that establish the specific behavior the device is allowed to have while connected to a network.
At ForeScout, we don’t believe in artificial barriers that limit your options and force vendor lock-in. CounterACT works with leading network infrastructure, third-party security and IT management solutions. It also offers flexible deployment and configuration options to match your company’s specific needs. Choose physical or virtual deployments or both, and centrally manage them with CounterACT Enterprise Manager.
Several features set CounterACT apart:
- Agentless: No endpoint agents are required for authentication and network access control, allowing CounterACT to see and control managed, unmanaged and IoT devices.
- Open interoperability: CounterACT works with popular switches, routers, VPNs, firewalls, endpoint operating systems (Windows®, Linux, iOS®, OS X and Android), patch management systems, antivirus systems, directories and ticketing systems—without infrastructure changes or upgrades.
- Security orchestration: Optional modules orchestrate information sharing and policy-based security enforcement between CounterACT and leading IT and security management products.
- 802.1X authentication, or not: Choose 802.1X or other authentication technologies such as LDAP, Active Directory, RADIUS, Oracle and Sun. Hybrid mode lets you use multiple technologies concurrently.