Categories
Problems that solves
No IT security guidelines
Risk or Leaks of confidential information
Unauthorized access to corporate IT systems and data
Malware infection via Internet, email, storage devices
Non-existent or decentralized IT incidents' management
Risk of attacks by hackers
Risk of data loss or damage
Non-compliant with IT security requirements
Insufficient risk management
Values
Ensure Security and Business Continuity
Ensure Compliance
Manage Risks
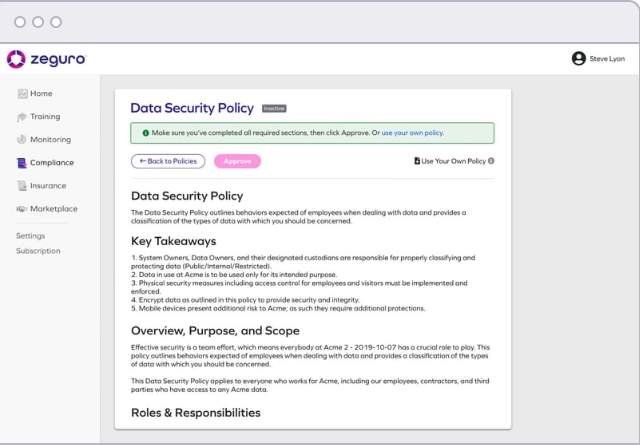
Zeguro Cyber Safety
Stop cyber threats before they start with web app vulnerability scanning.
Description
Monitoring
Set up automated scans in minutes.
Reduce web-based risks.
Stay in compliance.
50% of SMBs have experienced a web-based attack.
According to Ponemon Institute’s most recent Global State of Cybersecurity in SMBs, web-based attacks are the second most common cyberattack experienced by SMBs. Hackers take advantage of web vulnerabilities, outdated software, and configuration errors to infiltrate your web applications and gain access to sensitive data. Securing your web applications, which includes your public-facing website as well as any web applications your customers might log into, is imperative to keeping your business and your customers’ data safe.Protect your web applications from hackers
Web app vulnerability scanners look for weaknesses in your web apps so they can be fixed before they’re exploited by hackers. Zeguro’s Monitoring module makes web app scanning quick, easy, and customizable. Choose between lightning and normal scan levels and a monthly or quarterly cadence. You can even schedule your scan for a specific day and time. Once scans are completed, you’ll get clear, actionable results. The downloadable report prioritizes vulnerabilities based on criticality, and includes evidence showing where each vulnerability exists along with a set of suggested fixes.Protect your business through people, process, and technology. With Zeguro Cyber Safety, you will also get access to:
Training
Security Policies
Insurance
Scheme of work