Categories
Problems that solves
No control over data access
Inability to forecast execution timelines
Unauthorized access to corporate IT systems and data
Risk or Leaks of confidential information
Employee personal use of corporate IT during working hours
Malware infection via Internet, email, storage devices
High costs of routine operations
Low employee productivity
HR management
Customer attrition
Low quality of customer support
Shortage of information for decision making
Poor communication and coordination among staff
No control over implementation
Values
Enhance Staff Productivity
Ensure Security and Business Continuity
Support Decision Making
Enhance Competitive Ability
Reduce Production Timelines
Teramind Starter
Employee Monitoring Software with Powerful Insider Threat Detection and Productivity Analysis Features
Description
Teramind Starter: Employee Monitoring Simplified
Teramind Starter is Teramind’s entry-level employee monitoring solution. It’s built on top of Teramind’s award-winning UAM and DLP platform and includes powerful features such as real-time activity tracking, video capture and playback, and a set of productivity optimization tools. While it packs a punch in terms of functionality, it’s designed to be super affordable for the budget sensitive startups and small businesses looking for entry level employee monitoring, user session recording and process optimization capabilities.
Teramind Starter is a Feature-Rich Employee Monitoring Solution with Tangible Business Benefits
Monitor Employee Activity in Real-Time
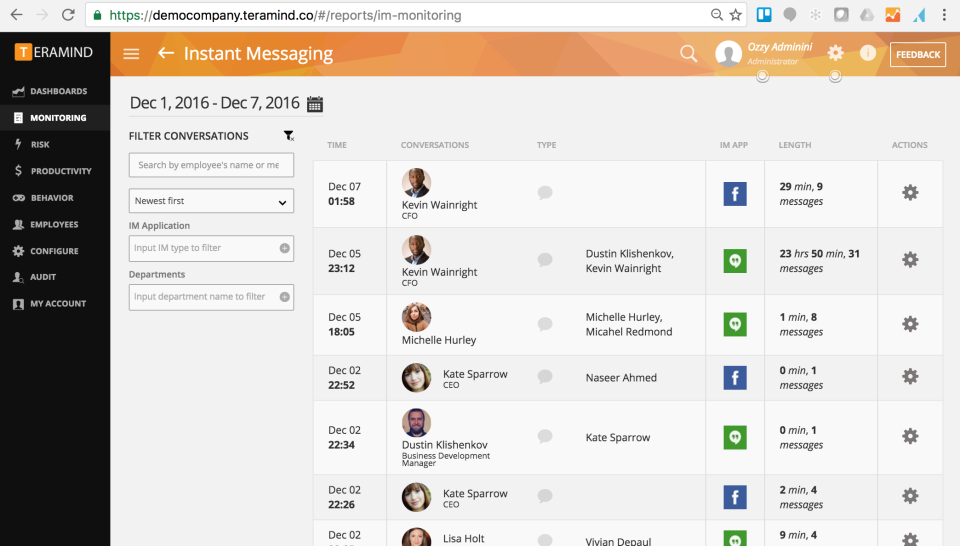
Employees spend majority of their time on desktop using apps or websites. Teramind Starter lets you visually records every action that a user makes on their desktop (screen), apps, websites, social media and instant messengers. Capture all the essential activity data like application/site name, URL, duration etc.- all from the industry's most powerful and user-friendly employee monitoring dashboard.
- Ensure Employee Privacy with Adjustable Tracking
Each monitored object like screen/apps/websites etc. can be configured to take into consideration what needs to be monitored and measured and who has access to the monitored records. You can control who you want to monitor, how much you want to monitor, when and for how long. This allows for instant administrative control to respect employee privacy requirements.
- Detect Insider Threats with Intelligent Policy & Rules Engine
Determine what behaviors are high risk i.e. downloading files and attachments from unknown website, running a risky application etc. Then, apply behavior-based rules to detect when users violate the rules. The system will automatically block harmful employee activity or warn the user with a customized message about potential danger reducing false positives with minimal supervision. The system can also notify you about sensitive rule violation incidents that needs your personal attention.
- Boost Employee Productivity and Increase Organizational Performance
Use the workforce productivity tools to track active vs inactive time, late shifts, long breaks etc. Use intelligent activity-based rules to automatically identify clues to customer dissatisfaction (angry sentiments in social media posts/ customer query in instant messenger not answered etc.) and implement processes to provide better service.
- Monitor Privileged Users for Extra Security
Teramind allows organizations to create profiles for remote and privileged employees and then define what information and system resources each profile can access. Create autonomous rules to notify the authorities of any suspicious privileged user activity, such as unscheduled login, access to system configuration, creation of backdoor accounts etc.
- Audit Security Incidents with Forensics
Detailed alerts for all users can be viewed including any security event and what action was taken, which app/site was involved, what data got accessed etc. Session recordings and history playback can be used to view user’s desktop or exported as MP4 video to be used as evidence in any investigation. Immutable system logs and session reports provide with further information to trace back to the source and cause of any security incident.
Scheme of work