View
Sorting
Products found: 9
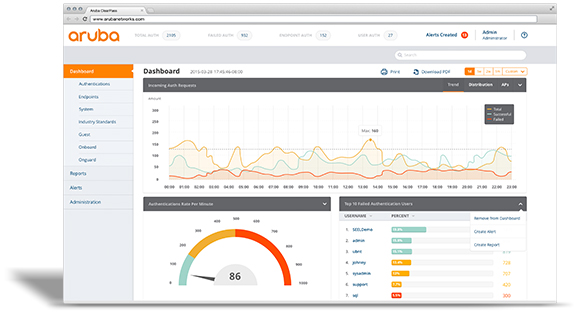
Aruba ClearPass
ClearPass allows you to safely connect business and personal devices to your network in compliance with your security policies. It allows you to grant full or limited access to devices based on users’ roles, device type, and cybersecurity posture.
This solution leverages the next plan:
Identify
With this new demand for network access, the burden on your IT department has increased exponentially and it’s not just laptops and smartphones that should be on your radar. IoT devices, printers, and even surveillance cameras are connecting to companies’ wireless networks.
ClearPass helps you identify which devices are being used, how many are connected to your network, where they’re connecting from, and which operating systems are supported. It gives you continuous visibility into changes on your network, including which devices are connecting and disconnecting.
When you need device-specific information, you can easily identify a device’s:
- Type and model name
- MAC address
- IP address
- NIC vendor
- OS and version number
- VLAN
Enforce
Enforcing network policies can pose a huge challenge to IT departments. When an employee wants to add a new device to the network, they often have to go through extensive IT protocols. They may even need someone from IT to walk them through the process.
ClearPass allows you to enforce policies during the onboarding of new devices without any involvement from your IT department – whether it’s a laptop, smartphone, or security camera. A built-in certificate authority lets you support devices more quickly without any additional IT resources.
Your IT team will simply need to establish your foundation of security and write rules that define:
- Who can onboard a device
- The type of device users can onboard
- How many devices each user can onboard
You can then enforce access a number of ways. You can use a portal, or you can use the more secure and preferred method that uses encryption in the authentication process. After devices are granted access, ClearPass uses active and passive profiling methods to monitor your network and keep it safe.
Protect
The health of individual devices connected to your network is an essential component of network security. With ClearPass OnGuard, your IT team can define the “level of health” a device must have in order to gain network access.
This solution automatically conducts critical endpoint health checks and posture assessments to ensure that all devices are compliant with your requirements (and industry best practices). It works for both wired and wireless networks.
ClearPass also offers a variety of third-party integrations (which we’ll touch on shortly). These integrations empower you to implement dynamic policy controls and threat remediation. You’ll have real-time insight into the activity on your network, equipping you to identify and address any threats that may present themselves.
After all, you have to be prepared to take action if you discover unusual network behavior. That requires establishing a unified approach that can block traffic and disconnect devices when necessary – even in the middle of the night.
Integrate
The right network security solution must be comprehensive and that often requires you to create a seamless solution comprised of several different platforms.
Aruba ClearPass Exchange integrates with over 25 IT partners – the vast majority of your current technology and security stacks - to ensure that every element of your system is working without issue.
These third-party technology systems could include:
- Firewalls
- Enterprise mobility management (EMM)
- Mobile device management (MDM)
- Security information and event management (SIEM)
Whichever platforms you use (or are considering), they will work with ClearPass’ REST-based APIs, Syslog messaging, and extensions repository. Your collective solution will deliver end-to-end policy enforcement and the visibility you need to keep your network secure.
Source: inbound.kelsercorp.com/blog/what-is-aruba-clearpass-and-how-does-it-protect-your-network
Cisco Identity Services Engine
CISCO ISE (Identity Services Engine)
The Cisco Identity Services Engine (ISE) offers a network-based approach for adaptable, trusted access everywhere, based on context. It gives you intelligent, integrated protection through intent-based policy and compliance solutions. And it is all delivered with streamlined, centralized management that lets you scale securely in today's market.
Username is a key element in determining access to a network. Username can also help you alert you users to potentially suspicious activity with their devices. It answers the all-important question of who is connected to your network.
The Cisco Identity Services Engine (ISE) Passive Identity Connector centralizes, consolidates, and distributes identity information, including IP addresses, MAC addresses, and usernames. At the same time it offloads work from key infrastructure such as Microsoft Active Directory.
Many servers on the network are active participants in user authentication. They take user credentials and either verify them or look them up in a dedicated repository such as Active Directory. Rather than being actively involved in user authentication, the Passive Identity Connector listens to the various authentication servers on the network. It centralizes the authentication information, becoming the single source of truth for its subscribers.
The Passive Identity Connector distributes the session identity information to other devices on the network that are natural consumers of such information. These devices include firewalls, web security appliances, and traffic analyzers. Using the Cisco Platform Exchange Grid (pxGrid), the Cisco ISE Passive Identity Connector can support up to 20 subscribers.
Features:
- Centralized information
- Improved performance
- Syslog server support
- Active Directory support
- Kerberos SPAN support
- Endpoint probes
- Active Directory agent
- Support for custom APIs
- Citrix Terminal Server support
- High availability
- Migration support
- Virtual machine support
- Scalability
Benefits:
- Consolidates data from multiple authentication sources, eliminating the need for every system that requires authentication data to interact with every authentication source
- Eliminates the burden on an often-overtaxed infrastructure with a single system that caches data for other authentication data consumers
- Gathers authentication data from systems that support syslog
- Gathers authentication data from Active Directory through the Microsoft Windows Management Interface (WMI)
- Gathers Active Directory authentication data from switches supporting Kerberos SPAN
- Understands when endpoints log off
- Gathers authentication data from up to 10 Microsoft Active Directory domain controllers
- Gathers authentication data from systems that support a custom interface
- Gathers authentication data from Citrix Terminal Server
- Supports active/passive redundancy
- Customers may upgrade from the Cisco ISE Passive Identity Connector to Cisco ISE, adding the Passive Identity Connector node to an existing Cisco ISE cluster.
- Supports KVM, VMware, and Hyper-V
- Tailored to fit your organization with support for 3,000 and 300,000 sessions
ForeScout CounterACT
CounterACT agentless technology discovers, classifies and assesses devices. CounterACT interrogates the network infrastructure to discover devices as they connect to the network. Our customers have reported seeing up to 60% more devices on their network than previously known. After discovering a device, CounterACT uses a combination of passive and active methods to classify the device according to its type and ownership. Based on its classification, CounterACT then assesses the device security posture and allows organizations to set policies that establish the specific behavior the device is allowed to have while connected to a network.
At ForeScout, we don’t believe in artificial barriers that limit your options and force vendor lock-in. CounterACT works with leading network infrastructure, third-party security and IT management solutions. It also offers flexible deployment and configuration options to match your company’s specific needs. Choose physical or virtual deployments or both, and centrally manage them with CounterACT Enterprise Manager.
Several features set CounterACT apart:
- Agentless: No endpoint agents are required for authentication and network access control, allowing CounterACT to see and control managed, unmanaged and IoT devices.
- Open interoperability: CounterACT works with popular switches, routers, VPNs, firewalls, endpoint operating systems (Windows®, Linux, iOS®, OS X and Android), patch management systems, antivirus systems, directories and ticketing systems—without infrastructure changes or upgrades.
- Security orchestration: Optional modules orchestrate information sharing and policy-based security enforcement between CounterACT and leading IT and security management products.
- 802.1X authentication, or not: Choose 802.1X or other authentication technologies such as LDAP, Active Directory, RADIUS, Oracle and Sun. Hybrid mode lets you use multiple technologies concurrently.
FortiNet FortiNAC
- Network visibility to see every device and user as they join the network
- Network control to limit where devices can go on the network
- Automated response to speed the reaction time to events from days to seconds
PATRIOT Network Security Solutions Provider
- Оставаться на связи с сотрудниками, партнерами и клиентами
- Придерживаться применимых правил соответствия ИТ
- Держать все данные и инфраструктуру защищенными от злонамеренных атак
- Включить мобильность и виртуализацию в вашей организации
- Избегать бесполезного устранения вредоносного ПО и системных сбоев
Patriot Network Security Solutions Provider
- Stay securely connected with employees, partners and customers
- Adhere to applicable IT compliance regulations
- Keep all data and infrastructure protected from malicious attacks
- Enable mobility and virtualization across your organization
- Avoid time-wasting malware remediation and system outages
Portnox CLEAR
- Single-pane-of-glass visibility for endpoints in use in all locations and at all times
- Protects the network from vulnerabilities arising from the mobile workforce, BYOD, IoT
- Easy to deploy, with a pre-set infrastructure that requires no prior training
- Cloud-based and fully scalable, requiring absolutely no hardware
- Flexible subscription-based pay-as-you-go model to fit the needs of the growing enterprise
- Secure of all access layers–wired, wireless, and virtual
- Multi-factor authentication over the VPN based on user identity and device risk score
- Continuous risk monitoring that identifies vulnerable end points and takes automated actions
Portnox CORE
- See relevant security risks on the network.
- Control access to ensure compliance with security protocols.
- Automate reactions based on device and user behavior to prevent breaches.
The ROI4CIO Product Catalog is a database of business software, hardware, and IT services. Using filters, select IT products by category, supplier or vendor, business tasks and problems. Find the right business solutions by using a neural network search based on the results of deployment products in other companies.